Abstract
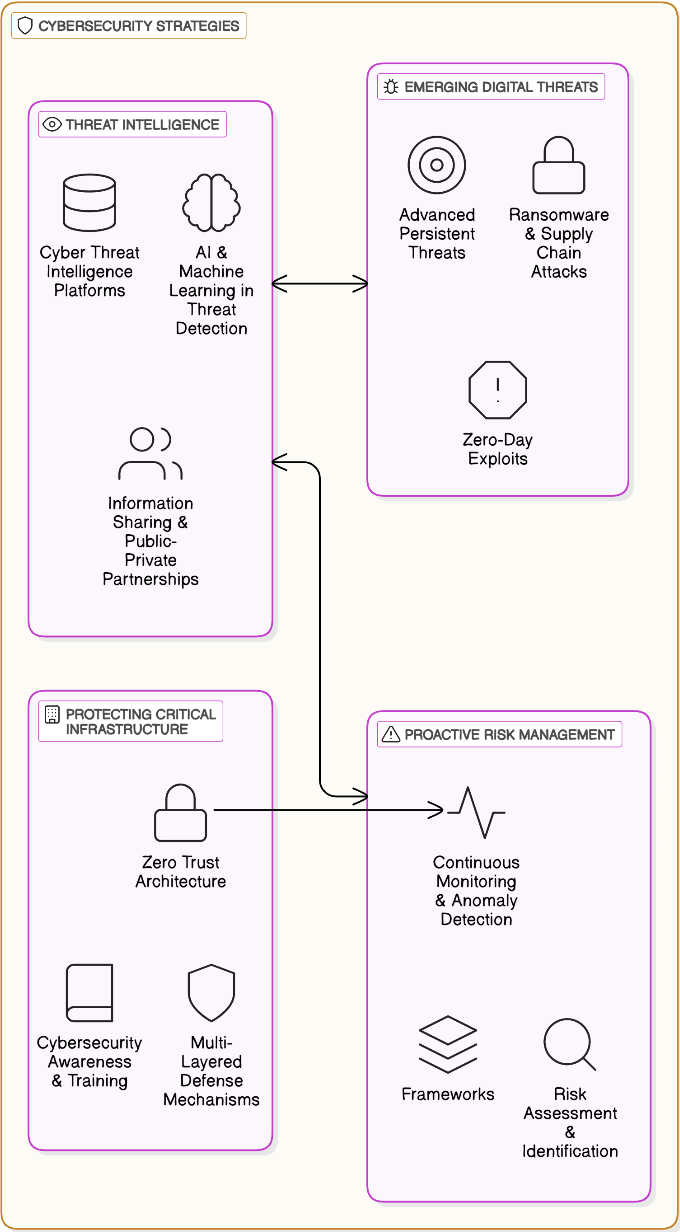
The rapid evolution of digital threats is a major hurdle to the security of vital infrastructure, driving the need for advanced cybersecurity methods like those based on the use of new technologies. This research seeks to assess the use of neural networks in cybersecurity and especially the role of these technologies in proactive risk management and threat intelligence. Neural networks, mainly deep learning models, had excellent success in detecting, analyzing, and mitigating all cyber threats with no time delay. Through the integration of sophisticated components such as pattern recognition, anomaly detection, and predictive analytics, these models improve threat detection accuracy while minimizing false positives. The review of the latest neural network models applied in cyber security presented in this publication is the greatest, for example convolutional neural networks (CNNs), recurrent neural networks (RNNs), and transformer-based models, with a full analysis of how effective they are in protecting critical infrastructure. Furthermore, the connection of neural networks with security information and event management (SIEM) systems enabling automated threat responses and the continuous learning of evolving cyberattack patterns is also included in this paper. Some challenges are also addressed like adversarial machine learning, data privacy concern, and the implementation of Computational efficiency. It concludes by finding that the possibilities of using neural networks to increase cybersecurity resilience are remarkable and that such systems could be optimized in the future with AI for a solid, robust, and adaptive strategy for critical infrastructure protection.
Keywords
neural networks
critical infrastructure protection
threat intelligence
proactive risk management
adversarial machine learning
Data Availability Statement
Data will be made available on request.
Funding
This work was supported without any funding.
Conflicts of Interest
The authors declare no conflicts of interest.
Ethical Approval and Consent to Participate
Not applicable.
Cite This Article
APA Style
Ashraf, M., Ahmad, F., & Iqbal, I. (2025). Advanced Cybersecurity Strategies Leveraging Neural Networks for Protecting Critical Infrastructure against Evolving Digital Threats through Proactive Risk Management and Threat Intelligence. IECE Transactions on Neural Computing, 1(1), 44–54. https://doi.org/10.62762/TNC.2025.737491
Publisher's Note
IECE stays neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Copyright © 2025 by the Author(s). Published by Institute of Emerging and Computer Engineers. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (
https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.


 Submit Manuscript
Edit a Special Issue
Submit Manuscript
Edit a Special Issue
 Copyright © 2025 by the Author(s). Published by Institute of Emerging and Computer Engineers. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made.
Copyright © 2025 by the Author(s). Published by Institute of Emerging and Computer Engineers. This article is an open access article distributed under the terms and conditions of the Creative Commons Attribution (CC BY) license (https://creativecommons.org/licenses/by/4.0/), which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. 